What is token propagation?
Token propagation is the mechanism of securely passing an identity or access token (such as OAuth or JWT) from one service or application to another so that downstream systems can act on behalf of the original user or client without re‑authenticating. In business scenarios, this is commonly used in multi-tier applications where a front-end app calls multiple backend services, each needing to know “who” the user is and what they’re allowed to do. Typical use cases include single sign-on (SSO) across internal tools, orchestrating workflows across multiple APIs or microservices while preserving user context, enforcing fine-grained access control in data platforms, and enabling secure B2B integrations where partner systems call internal services using delegated permissions.
SnapLogic MCP Server and OAuth2
The SnapLogic MCP Server allows users to create, configure, and manage MCP Servers for integrating with external agentic systems with ease. SnapLogic MCP Server supports OAuth2 authentication policies that enable token propagation.
Hands-on
In this example, we will look at an MCP Server with an MCP Server pipeline with the JWT token available in the pipeline in raw form and resolved fields.
ⓘ The configurations in the example are for token propagation only and do not affect the MCP Server’s processing itself. However, the resolved claims must exist if they are used; otherwise, it will result in an error.
Components
- MCP Server with OAuth2 JWT Token Policy configured
- An MCP Server pipeline
1. Policy setup
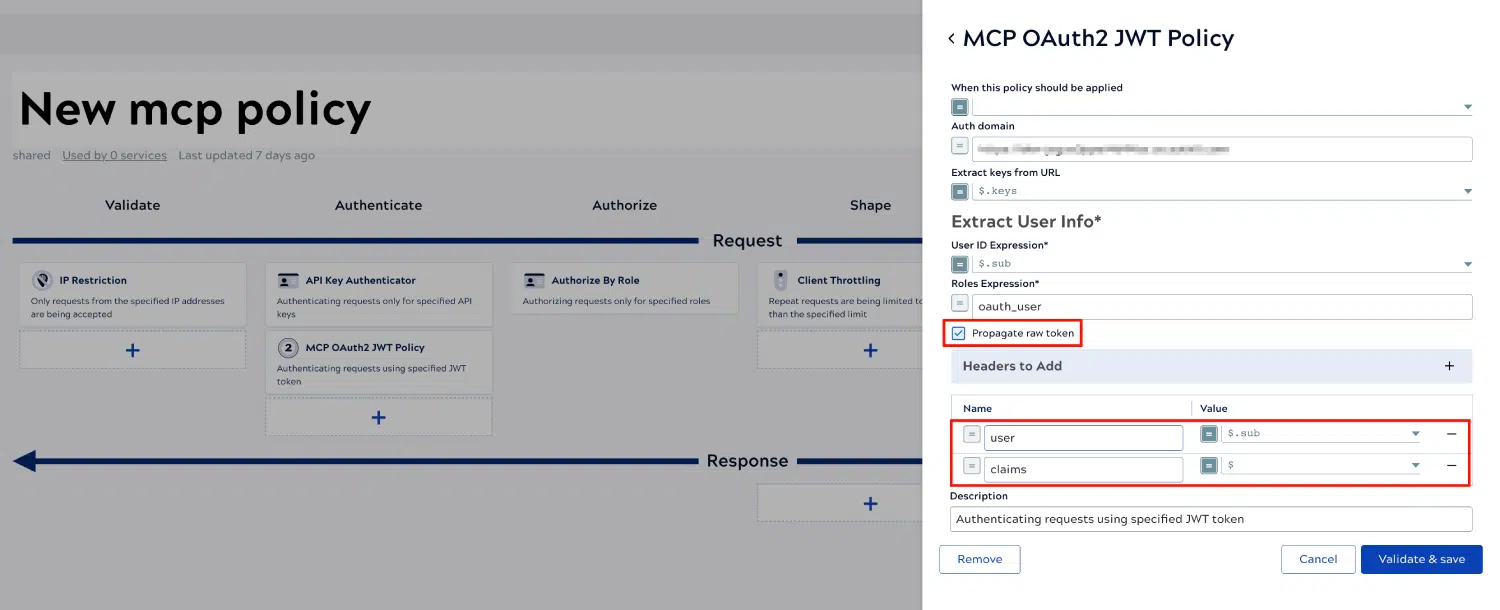
The MCP OAuth2 JWT Policy supports token propagation under two areas:
- Propagate raw token – This propagates the raw token to the pipeline parameters.
- Headers to Add – This extracts the claims in the JWT token, which fields can be extracted with an expression, e.g.,
$.sub, or the claims as a whole using$.
The fields will then be available in the pipeline if the corresponding pipeline parameters exist.
2. Pipeline setup
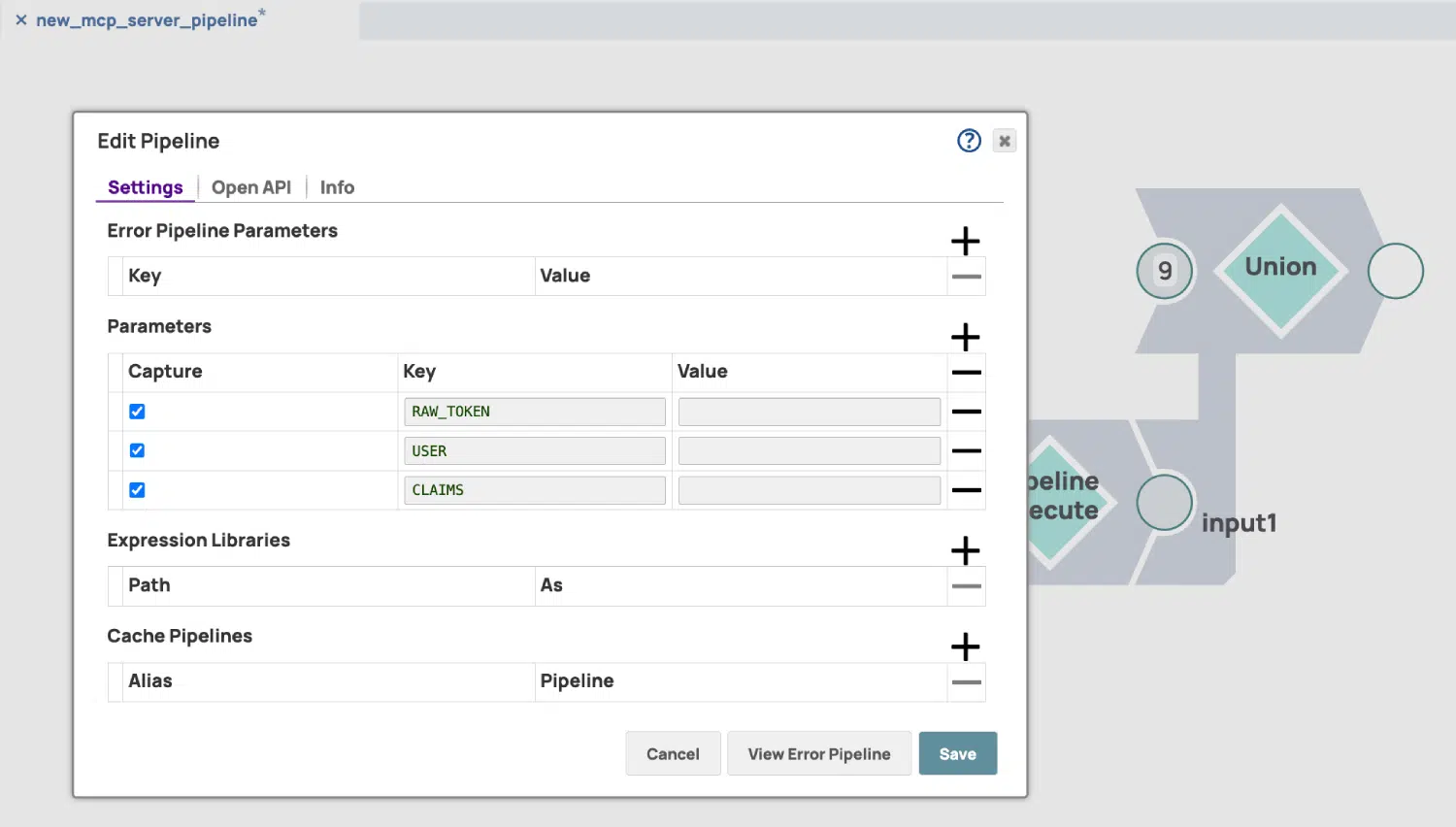
Now, after the policy is properly configured, we will need to add keys to the pipeline parameters so the values can be passed to the declared keys. In the policy, we enabled Propagate raw token and two extra Headers to Add: user and claims, so we have RAW_TOKEN, USER, and CLAIMS declared in the keys. Note that all keys must be in upper case for keys coming from the headers.
⚠️ The keys in the parameters must exist and match the fields in upper case in the policy. In addition, fields in the header with hyphens - will be changed to underscores _ in the pipeline parameters.
The keys in the parameters must exist and match the fields in upper case in the policy. In addition, fields in the header with hyphens - will be changed to underscores _ in the pipeline parameters.
These are the required configurations to enable token propagation. Users can now implement customized strategies in the pipeline for more granular control over tools to expose in the pipeline.